The Growing Need for Enhanced Security
In today’s digital landscape, where cyber threats are rampant, two-factor authentication (2FA) has emerged as a vital security measure. This feature provides an extra layer of protection that goes beyond traditional password security.
The increasing prevalence of cybercrime underscores the urgency of adopting robust security practices. Recent studies show that over 80% of data breaches involve stolen or weak passwords, leaving individuals and organizations vulnerable to malicious attacks. It is projected that cybercrime damages will escalate, with estimates reaching an astounding $10.5 trillion annually by 2025. This alarming trend highlights the need for proactive measures to safeguard sensitive information.
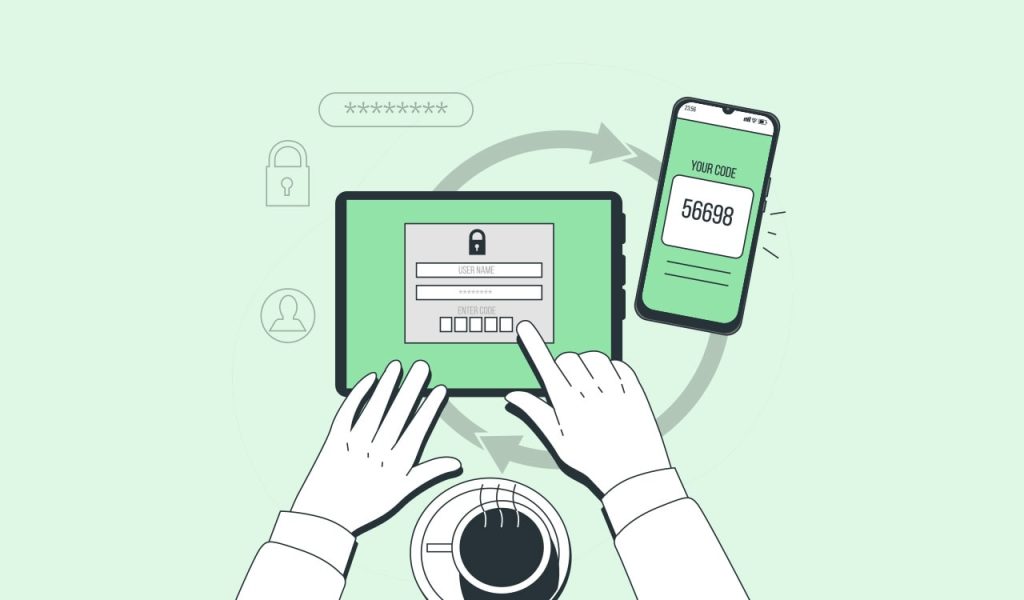
One of the most effective ways to enhance security is through two-factor authentication, a process that requires users to provide two distinct forms of identification before accessing their accounts. This typically involves something the user knows (like a password) and something the user has (such as a mobile device or security code). Importantly, accounts with 2FA enabled are significantly less likely to be compromised, adding a formidable barrier against unauthorized access.
Recognizing the necessity for heightened security, popular applications are rapidly adopting 2FA protocols. For instance:
- Google: Offers 2-step verification, allowing users to authenticate their identity through either a phone number or dedicated authenticator apps, enhancing account integrity.
- Facebook: Provides login alerts and 2FA options via SMS or authentication apps, alerting users to any suspicious activity in real-time.
- Banking Apps: Many banking institutions enforce 2FA as a standard practice for transaction approval and account management, ensuring that only authorized individuals can access financial assets.
The growing sophistication of cyber threats makes it imperative to understand how two-factor authentication works and why enabling it across your applications is essential. Not only does this safeguard your personal data from breaches, but it also plays a crucial role in fostering a safer online community for everyone. By taking the initiative to implement 2FA, you not only protect yourself but contribute to the overall security ecosystem, making it increasingly difficult for cybercriminals to succeed.
As the digital world continues to evolve, staying informed and vigilant is key. Consider taking the steps necessary to explore further how 2FA can bolster your online security and help you navigate the complexities of today’s cyber threats.
DON’T MISS: Click here for essential Wi-Fi security tips
Understanding the Mechanics of Two-Factor Authentication
At its core, two-factor authentication (2FA) is predicated on the principle of adding layers to security. This method stems from the recognition that relying solely on passwords is fraught with risk; passwords can be stolen, guessed, or compromised through phishing attacks. By demanding a second form of verification, 2FA substantially mitigates these risks.
But how does it actually work? When attempting to log into an application that utilizes 2FA, a user first enters their username and password—an action familiar to anyone who has navigated the digital landscape. Upon submitting these credentials, the system prompts the user for a second factor. This might manifest in various forms:
- SMS Codes: A numeric code sent to a registered mobile phone number that the user must enter to complete the login process.
- Authentication Apps: Tools such as Google Authenticator or Authy generate time-sensitive codes, providing an additional layer of security without relying on mobile networks.
- Biometric Data: Technologies like fingerprint scanning or facial recognition serve as a unique identifier, combining something the user is with something they know.
As these methods illustrate, two-factor authentication not only requires something the user knows (the password) but also something they possess (the mobile device or authenticator app), creating a dual barrier against unauthorized access. This dual requirement represents a significant leap forward in user account protection, as it virtually eliminates the likelihood that an unauthorized entity can gain entry, even if they have obtained the user’s password.
Moreover, the rise in popularity of 2FA in applications used by millions of individuals underlines its importance. For instance, platforms such as Dropbox, Twitter, and Amazon have integrated 2FA into their security protocols. This transition aligns with a heightened awareness of cybersecurity risks, which are often exacerbated by inadequate user practices, such as weak passwords or the reuse of credentials across multiple accounts.
This growing implementation is driven by more than just regulatory compliance; organizations are recognizing that the digital landscape requires a serious commitment to user security. Companies that take proactive steps in enhancing their security infrastructure are better positioned to protect sensitive data and maintain customer trust. In an era when consumer confidence is paramount, the presence of a robust security architecture can set a brand apart.
As users become increasingly aware of digital threats, embracing two-factor authentication will no longer be optional; rather, it will become a necessity. Individuals must take the initiative to enable this feature wherever possible, understanding that the effort required to set it up is minuscule compared to the potential damages that could result from an account breach. With the stakes higher than ever, now is the time to prioritize security and take advantage of protective measures like 2FA.
The Importance of Two-Factor Authentication in Popular Applications
In the modern digital landscape, securing personal information has never been more crucial. The need for robust security measures is underscored by the increasing frequency of hacking incidents and data breaches. Two-Factor Authentication (2FA) adds a vital layer of security that goes beyond traditional password protection.
One considerable aspect of 2FA is its ability to drastically reduce the risk of unauthorized access. When users enable 2FA on their accounts, even if a malicious actor manages to obtain their password, they cannot access sensitive information without the second form of authentication, usually a temporary code sent via SMS or generated by an app. This is especially relevant for popular applications such as email services, social media platforms, and banking apps, where personal and financial information is stored.
Furthermore, the implementation of 2FA can enhance user confidence. Knowing that there is an additional protective measure helps individuals feel more secure when navigating online environments. This is particularly important for businesses that collect sensitive user data; adopting 2FA can foster customer trust and potentially lead to increased user engagement.
| Category 1 | Category 2 |
|---|---|
| Security Enhancement | Prevents unauthorized access even if a password is compromised. |
| User Trust | Increases user confidence in the safety of their data. |
Adopting two-factor authentication isn’t just a technical decision; it’s a necessary step to ensuring the safety of individuals and businesses alike. As threats evolve, so must our security measures, making 2FA an indispensable element in the fight against cybercrime.
LEARN MORE: Click here to enhance your understanding of cloud security
The Broader Implications of Two-Factor Authentication
As cybersecurity threats continue to evolve and become more sophisticated, the incorporation of two-factor authentication (2FA) is not merely a matter of enhancing security but a critical measure for protecting personal and sensitive information. The implications extend beyond individual safeguarding, impacting businesses, organizations, and even national security.
To illustrate, consider the rise in data breaches in recent years. According to a report from Verizon, over 43 percent of data breaches involve small businesses, primarily due to resource constraints which lead to inadequate security measures. When a business opts for 2FA, they’re not only protecting their own data but also their customers’ sensitive information. This adoption creates a ripple effect, potentially safeguarding the entire digital ecosystem in which customers interact. A compromise in security at one business can lead to a domino effect, where customer data is exploited, resulting in loss of trust and financial implications for multiple parties involved.
Popular applications like Facebook and Google have reported increased security through 2FA implementations. Facebook’s Cybersecurity team noted a substantial decrease in unauthorized access once 2FA was made mandatory for certain users. This data showcases that when businesses strengthen their authentication systems, they foster a more secure environment for users, encouraging them to trust the platform with their information.
Furthermore, considering the shift towards remote and hybrid work cultures, the role of 2FA has become even more paramount. As employees access company data from various locations and devices, they become more vulnerable to phishing and other cyber threats. Enabling 2FA adds a layer of defense, especially in environments where the traditional corporate firewall is no longer in place. Security measures need to evolve in tandem with workplace practices, and 2FA serves as a valuable tool in this transition.
Critically, the deployment of 2FA is not without its challenges. Users may find it inconvenient, especially if they have to manage multiple codes or devices. However, the growing availability of user-friendly solutions, such as browser-based authentication, SMS or app-based codes, and biometrics, has streamlined the process, encouraging broader adoption. A survey conducted by LastPass suggests that users who implement 2FA feel more secure about their online presence, with 93% affirming its importance for safeguarding accounts.
Additionally, regulatory frameworks are evolving to prioritize user data security. In the United States, laws like the California Consumer Privacy Act (CCPA) and requirements stemming from the Health Insurance Portability and Accountability Act (HIPAA) underscore the need for robust security measures. As regulators push for stronger privacy protections, the implementation of features like 2FA within applications is increasingly necessary to comply with legal obligations and avoid penalties.
Ultimately, the future of digital authentication appears to be trending towards multifactor solutions, with 2FA leading the charge. As more applications adopt these practices, user education becomes essential. Familiarizing oneself with 2FA and the varying forms of security becomes a crucial step in maintaining personal security in a world where threats are omnipresent. This proactive approach empowers individuals and organizations alike to navigate the digital landscape with greater confidence.
DON’T MISS OUT: Click here to enhance your Wi-Fi security
Conclusion: Embracing Two-Factor Authentication for Enhanced Security
In an era marked by escalating cybersecurity threats, the significance of two-factor authentication (2FA) in popular applications cannot be understated. As we have explored, the adoption of 2FA not only bolsters individual account security but also fortifies the backbone of trust that underpins online interactions. Organizations, both large and small, must recognize that their vulnerabilities can have cascading effects, potentially compromising entire customer bases. The statistics are compelling; with over 43% of data breaches linked to small businesses, enhancing security through 2FA is not merely advisable but imperative.
Moreover, the transition to remote work environments has made the implementation of 2FA even more critical. Employees are accessing sensitive data from various locations, which heightens the risk of unauthorized access. By integrating 2FA, organizations can add an essential layer of protection against potential breaches while adapting to the evolving landscape of work and data access.
As regulatory frameworks tighten around data privacy, incorporating 2FA is not just a recommendation but often a requirement to comply with laws like the California Consumer Privacy Act (CCPA). In this digital age, the onus falls on both users and organizations to prioritize security measures that can significantly mitigate risks.
Ultimately, as we move towards a future where multifactor authentication becomes the standard, education about 2FA and its benefits is vital. Making informed choices about security measures empowers users and organizations to traverse the digital landscape confidently, safeguarding sensitive information against evolving threats. The journey toward cybersecurity is ongoing, but by embracing 2FA, we take a significant step in fortifying our cyber resilience.
Related posts:
Wi-Fi Network Security: Tips to Protect Your Connected Devices
How to Avoid Phishing in Instant Messaging Apps
Privacy in Social Media Apps: How to Protect Your Personal Information
How to Identify and Avoid Malicious Apps on Your Device
How to Protect Your Devices from Malware in Download Apps
Cloud Security: Protecting Your Files and Sensitive Data
Beatriz Johnson is a seasoned tech writer and digital tools expert with a passion for simplifying the complexities of technology and mobile applications. With over a decade of experience in the tech industry, she specializes in topics like productivity apps, software reviews, and emerging digital trends. Through her work, Beatriz empowers readers to make informed technology choices and stay ahead in the ever-changing world of apps and innovation.